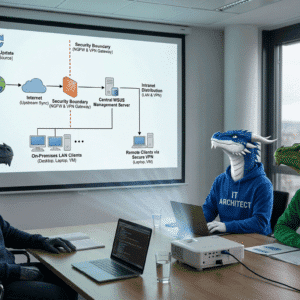
While our first part focused on the cloud-native way using Azure Portal and Policy, many IT administrators still prefer or require the reliability of on-premises control. In a traditional IT world, Windows Server Update Services is a legimate standard tool for server maintenance and Azure Arc Auto Updates using WSUS and GPOs.
Table of Contents
Introduction to Azure Arc Auto Updates using WSUS
Integrating the Azure Arc Agent into your existing Windows Update infrastructure allows you to maintain the 12-month support window without learning entirely new tooling. This part of our story focuses on how to leverage Group Policy Objects (GPOs) to ensure your on-premises servers take care of their own Arc Agent updates.
To get started with GPOs i recommend my series on GPOs foundations and how to implement your initial automation using GPOs.
The classic approach: Why Windows Update?
Using Windows Update (or Microsoft Update) for the Arc Agent is a bridge between the old and the new.
It is particularly useful if you:
- Manage servers in a highly regulated (maintenance windows) or highly restricted environment (no Azure Governance yet).
- Use established internal patch management workflows (WSUS or MECM).
- Want to ensure the Arc Agent is updated alongside other Microsoft products like SQL Server or Exchange.
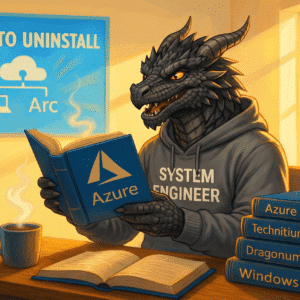
Technical deep-dive: Enabling Microsoft Update via GPO
Important: By default, Windows Update only looks for Windows OS patches. To get the Azure Connected Machine Agent, we must tell the OS to look for “other Microsoft products.” This method requires that your servers have a way to reach the Microsoft Update service, either directly via the internet or through an internal update server like WSUS.
To automate this across your domain, you don’t want to click a checkbox on every single server. We use a GPO to flip the switch for “Microsoft Update.”
The setting we are looking for is part of the standard Windows Update administrative templates. When enabled, it allows the client to scan for additional product catalogs, including the Azure Connected Machine Agent.
A new policy for this setting is created and I am following my naming convention and “one policy per configuration” mindset from my blog article with GPO background information.
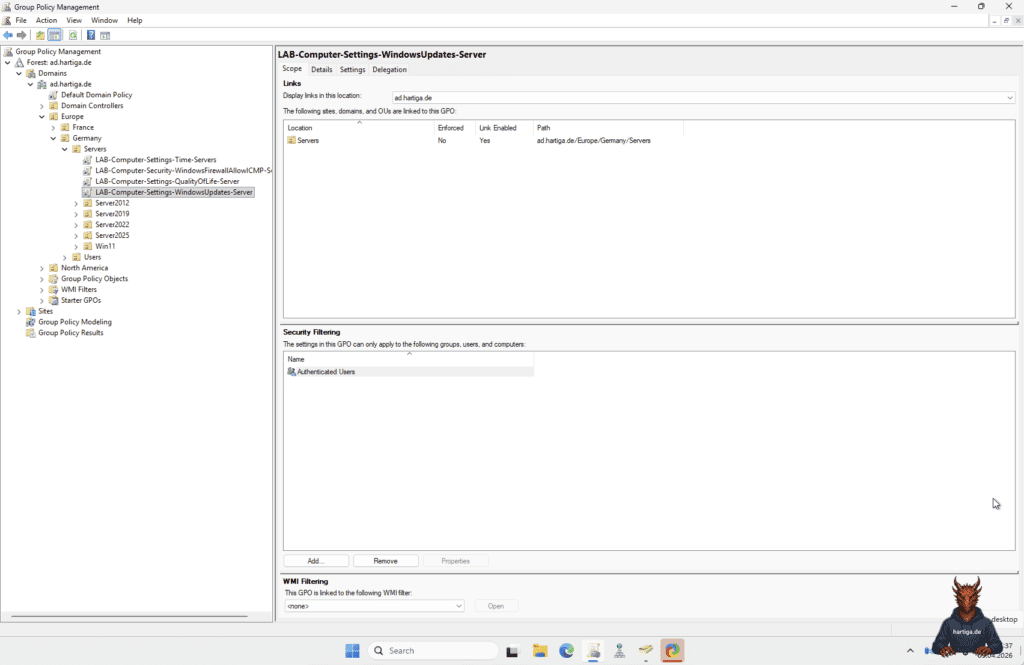
Lets configure the GPO to automatically update the systems in the OUs with the GPO associated and use Client-Side Targeting for the WSUS Computer Group HomeLab. Check my WSUS article for details on how this is configured here.
Step-by-step: Configuring WSUS or Configuration Manager
If you are using WSUS or Microsoft Endpoint Configuration Manager (MECM), simply enabling the GPO isn’t enough. You need to tell your update server to actually download and distribute the Arc Agent packages.
- Open the WSUS Administration Console or Configuration Manager.
- Navigate to Options and select Products and Classifications.
- Under the Products tab, look for the following: Azure Connected Machine Agent
- Check the box for this product (and all sub-options).
- Under the Classifications tab, ensure you have selected: Critical Updates & Updates
- Perform a synchronization.
- Once synced, you can approve the agent updates for your specific computer groups just like any other patch.
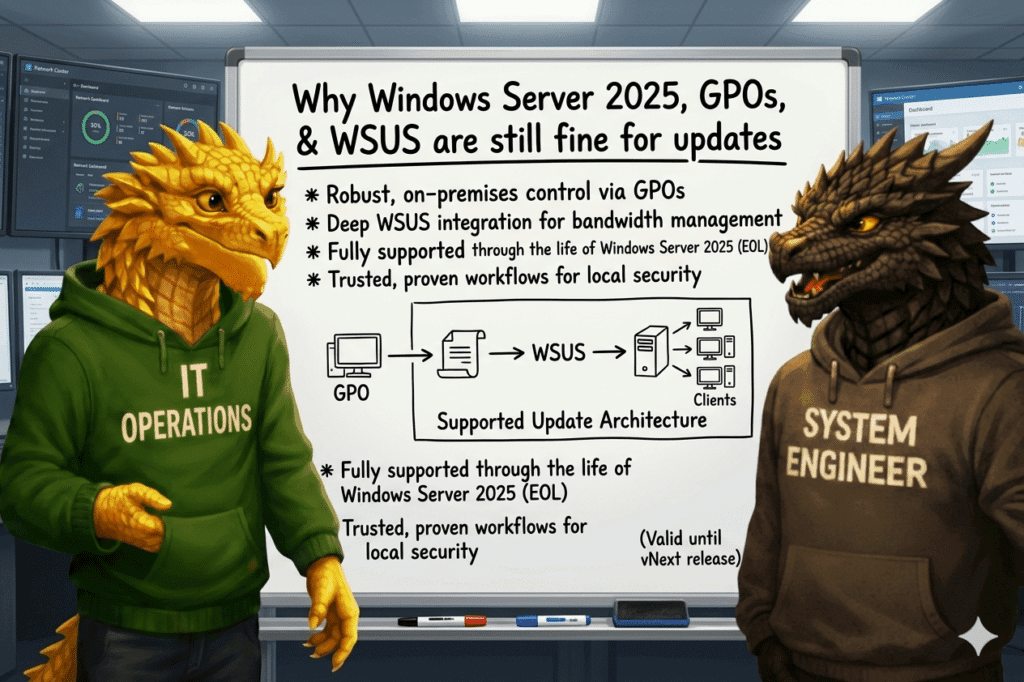
Important: WSUS is deprecated as part of Windows Server 2025. This is a sign for you to consider other options for mid to long term. Using WSUS at this point in time is perfectly fine.
My recommendations for Azure Arc Auto Updates using WSUS
Align your Update Groups to match your WSUS or MECM update groups with your Azure Resource Groups. This makes troubleshooting much easier.
Remember that 12-month Azure Arc Agent support limit. Even if you use GPOs, I recommend using an Azure Resource Graph query to proactively flag any agent that is approaching the 10-month mark or implement a monitoring with your prefered software management solution.
Don’t use both Azure Auto-Upgrade (from Part 1) and GPO/WSUS management simultaneously. While they can coexist, it makes troubleshooting a nightmare when an update fails. Choose one path based on where you want the “source of truth” to live.
Important: Check my guide “Windows Server 2025 – Part 9 (WSUS)” to see on how to install and configure WSUS on Windows Server 2025 or start my Windows Server 2025 Foundation and Homelab series here.
Conclusion on Azure Arc Auto Updates using WSUS
Whether you choose the modern Azure Portal approach or stay with the tried-and-true GPO method, the goal remains the same: staying supported and secure. By integrating the Azure Arc Agent into your existing Windows Update routine, you treat it like any other essential member of your server stack. Azure Arc Auto Updates using WSUS and GPOs is a valid approach.
Now that we have covered both the cloud-native and on-premises automation paths, your IT Operations and IT Security can hopefully only audit an Azure Arc server environment that is consistent and compliant.
Important: Remember the effect mentioned in my Foundation article. If you move a server out of a WSUS-managed OU, the registry keys for the update server will stay until you explicitly overwrite them or delete the keys via a cleanup script.
If you have any questions please don’t hesitate to reach out to me on LinkedIn, Bluesky or check my newly created Adaptive Cloud community on Reddit.
LinkedIn: https://www.linkedin.com/in/andreas-hartig/
Bluesky: https://bsky.app/profile/hartiga.de
Adaptive Cloud community on Reddit: https://www.reddit.com/r/AdaptiveCloud/
Additional Resources:
Updating the Azure Arc Agent (Connected Machine Agent) by Sarah Lean
Manage and maintain the Connected Machine agent
What’s new with Azure Connected Machine agent